Interestingly enough, a lot of potential cloud byers (i.e. internal IT or business functions) are not really familiar with basic concepts of proper and proven sourcing processes and methodologies, not to mentioned available “best practice” frame works for cloud and sourcing. The underestimated role of the due diligence concept, or even the knowledge of its existence, is just one prominent example.
 Already in 2013, the very well recognized Cloud Security Alliance (CSA) did rate “Insufficient Due Diligence” as one of the “Notorious Nine Cloud Computing Top Threats“. Actually, the risk of “Insufficient Due Diligence” is the only one risk not dedicated to security architecture and technology matters.
Already in 2013, the very well recognized Cloud Security Alliance (CSA) did rate “Insufficient Due Diligence” as one of the “Notorious Nine Cloud Computing Top Threats“. Actually, the risk of “Insufficient Due Diligence” is the only one risk not dedicated to security architecture and technology matters.
“Without a complete understanding of the CSP environment, applications or services being pushed to the cloud, and operational responsibilities such as incident response, encryption, and security monitoring, organizations are taking on unknown levels of risk in ways they may not even comprehend, but that are a far departure from their current risks.”
Sourcing lifecycle and due diligence
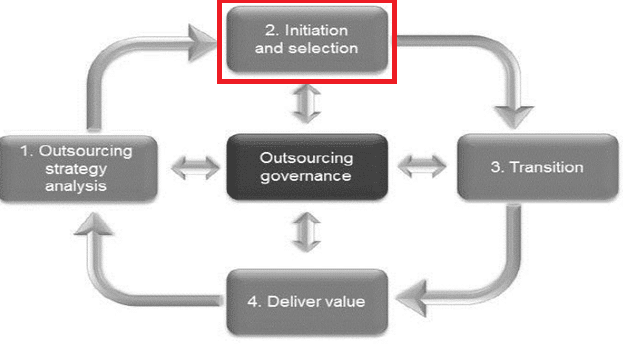
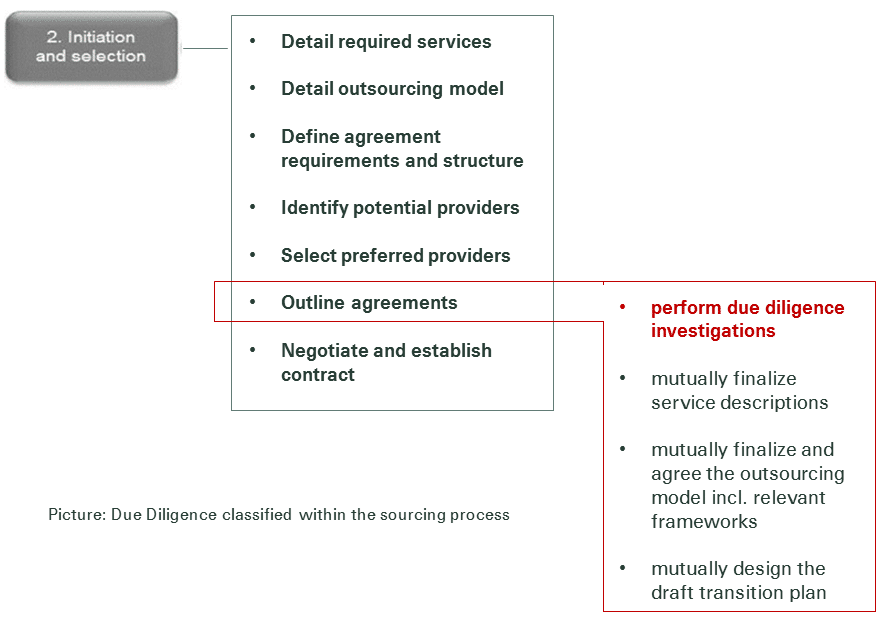
As per the just recently released international standard for outsourcing (ISO 37500:2014 “Guidance on outsourcing”), due diligence is an activity to be performed as part of the “2. Initiation and selection” sourcing lifecycle stage.
The ISO 37500 defines due diligence as “detailed assessment of one or more business processes or production lines, culture, assets, liabilities, intellectual property, judicial and financial situation in order to make an acquisition or obtain accountability”.
In short: the due diligence exercise in the sourcing process acts as the last quality gate for the instantiation of the business case of an upcoming sourcing engagements before contracting kicks-off.
Due Diligence and externally managed Cloud Services
What’s in scope for investigation when you have selected one or two cloud service providers before it comes to contracting?
Firstly, it is all about the confirmation of the information you have submitted to the service providers (rfp) and the validation of the information you have been given back by the services providers in the form of the rfp responses. It is all about mitigating the risk of wrong service scope, descriptions and SLAs and security definitions, service prices and governance models based on missing, incomplete and/or incorrect information. In particular for externally managed cloud services, data security and privacy concerns, compliance requirements, integration issues (network, identity & access, data, portal, APIs), end-user experience requirements (real-time, automated self-service) and service management requirements (processes, reporting, improvements) are on the agenda to be checked by the buyers. On the other side, service providers want to have their assumptions being confirmed in terms of service scope and priorities, integration and transition effort, volume and capacity information, organizational maturity and the upcoming operational governance model.
Commonly known due diligence methods
How to do due diligence? There are a couple of well-established vehicles supporting the goals of due diligence:
- Proof of Concept exercises, where cloud service providers demonstrate their capabilities within live demos of their services based on the buyers end-user expectations and integration requirements
- Service trial periods, user experiences labs (especially for SaaS)
- Reference visits and calls targeting the current customer base of a service provider
- Service provider site visits
- Provider audits (compliance and security)
- Mutual clarification workshops and access to all relevant data.
As a result of due diligence, both parties should have the confidence that risks have been mitigated and assumptions have been resolved in order to proceed with the next steps in the sourcing process. The results should be gathered in a signed due diligence report as a base for the upcoming agreements and the contract. Another outcome of the due diligence phase is the introduction of the future teams responsible for managing the service in transition and operation.. Team members from both sides will recognize culture and behavior in favor or in harm for future collaboration.
 Even when recognizing the speed and flexibility of the sourcing process for cloud services, undoubted, a good due diligence will build the base for the successful instantiation of the business case for both, the service customer and the service provider side.
Even when recognizing the speed and flexibility of the sourcing process for cloud services, undoubted, a good due diligence will build the base for the successful instantiation of the business case for both, the service customer and the service provider side.

Hi Ben,
I agree to the most ideas you have summarized for us.
But I think especially for SaaS some things are mixed up which we should not lump together.
Some of the capabilities (and the associated risks) are more related to the Software, and some are more related to the cloud delivery (sourcing) aspect. I agree it will be hard to differentiate between the pure software capabilities (features & functions) and the service capabilities (response times, etc.) for the user experience aspects.
Your article is mentioning two parties, but I think there should be more:
1. One is the user (service consumer). This group can evaluate and decide if the software is working or not.
2. One is the Technical Verifier. This party can verify all technical aspects.
3. One is the GRC manager, to prove risk, security and compliance.
4. One is the Service Integrator, who is responsible for data and process integration.
5. One is the service customer, who pays for the Service.
6. Another one is the Service Provider.
7. And another one is the Software Vendor, because many times he will differ from the Service Provider.
The last twenty years number 2 to 5 were combined in one IT Organization. Many aspects were covered and provided more or less hidden from the user. Eg. The three aspects of Security: Confidentiality, Integrity and Availability were always part of any service provided by internal IT.
But if the internal IT organization is not playing this role anymore, who is responsible for all this things? Who are the players in the due diligence report? I think the cook book you are providing is still missing some of the necessary cooks!